



Ransomware Timeline. Source: Morphisec
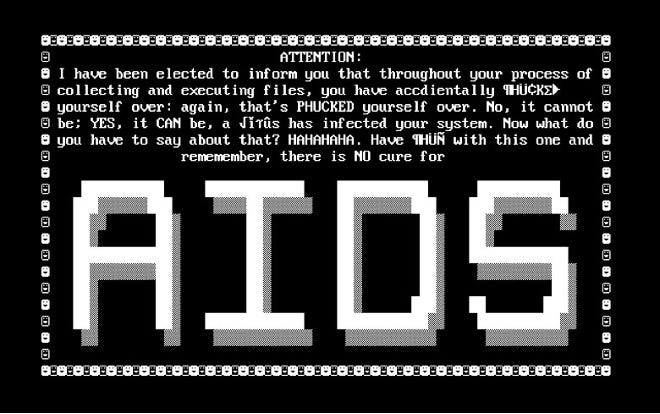
AIDS Trojan

GpCode

Archiveus
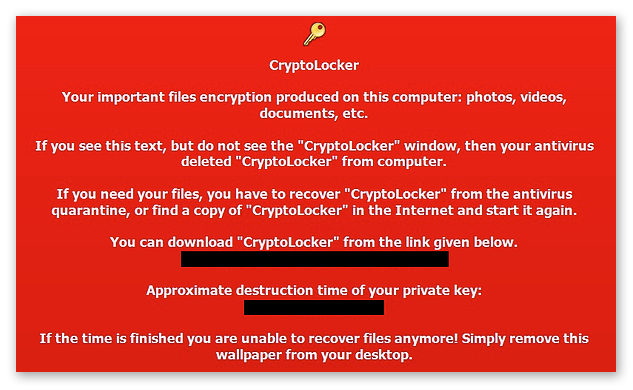
CryptoLocker

Tox Ransomware

Satan Ransomware

WannaCry

NotPetya

GandCrab

REvil Ransomware Note
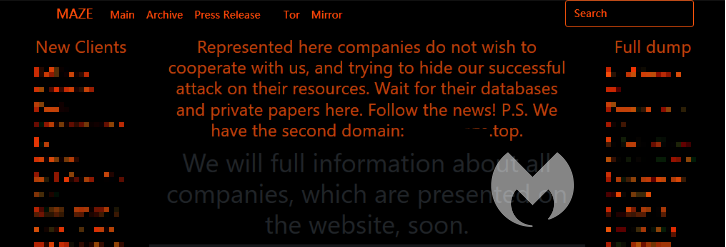
Maze

DarkSide Ransomware Note

Conti Leak Page

LockBit 3.0


BlackSuit Ransomware


Conti Internal Chat Leak



Underground forum post with details to download Volume 1 of the Ransomware Manual


Telegram Phishing Bot Demo